What does NetCloud SASE include?
Designed to be holistic yet modular, NetCloud SASE allows you to consume the services that you need, when you need them.
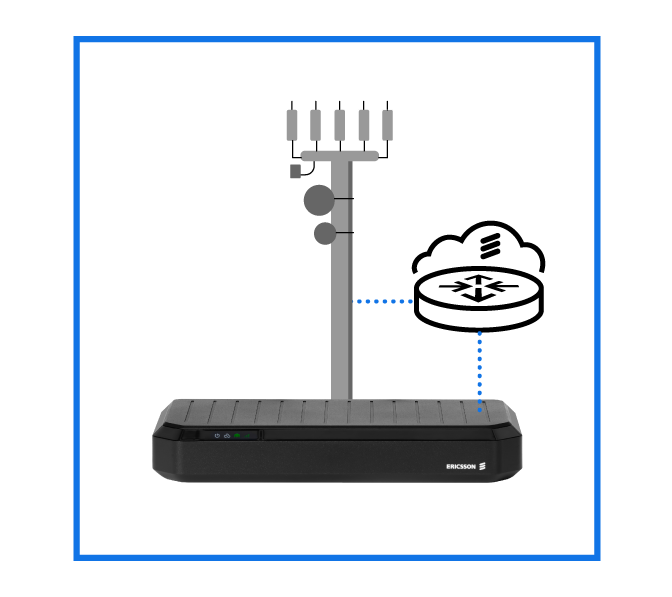
Ericsson NetCloud SASE
Next to bamboo, your network edge might be one of the fastest growing things on the planet (at least, it feels that way). Cellular is enabling agile connectivity for hard-to-reach people, places, and things. This expanding attack surface is difficult to secure. NetCloud SASE integrates cellular-centric SD-WAN and security into a fully unified, simple-to-use solution. It extends beyond fixed sites to secure dynamic environments where site locations are shifting, vehicles are moving, IoT devices are multiplying, and employees are working from anywhere.
Designed to be holistic yet modular, NetCloud SASE allows you to consume the services that you need, when you need them.
Zero trust SD-WAN
A simpler, more secure SD-WAN, optimized for cellular networks. Designed for providing an outstanding digital experience in environments where applications reside everywhere and require secure access from anywhere.

Zero trust security
Provides isolated, secure access to private applications or assets on the WAN for both managed and unmanaged devices (IoT, contractor devices, BYOD).
Cloud-first and lean IT companies can take advantage of Ericsson’s global cloud and have zero trust security and SD-WAN technologies delivered as a service managed through Ericsson NetCloud Manager.
Organizations preferring a local deployment option can take advantage of NetCloud Service Gateway, which can be deployed in the customer data center or private cloud environment. This solution offers SD-WAN and zero trust security services — all managed from NetCloud Manager. Explore the Service Gateway.