Public safety technology trends augment responders' vital services
How do police and EMS technology advancements maintain connectivity at critical times? Cellular, for starters Wireless public safety technologies will...
Get the latest info and insights about wireless edge networking using cloud-managed 5G and LTE for business solutions. Explore the reliability, flexibility, and security of cellular networks for branch, mobile, and IoT network deployments.
How do police and EMS technology advancements maintain connectivity at critical times? Cellular, for starters Wireless public safety technologies will...

When relying on 5G isn’t enough, LEO satellites fill critical coverage gaps for emergency services Public safety connectivity is evolving ...
For years, wireless has been considered as back-up connectivity, useful but secondary to wired WAN. Today, forward-looking organizations are building ...

The End of the "Blind Leap": Why Your 5G Strategy Needs a Reality Check In the enterprise world, we’ve been sold a bit of ...

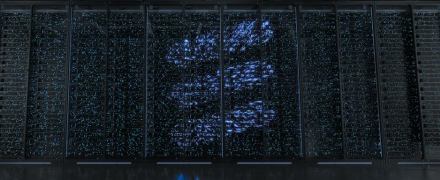
The future of enterprise AI depends on the network performance that a 5G foundation can provide AI and 5G are ...

Where modular design meets operational resilience to transform fleet connectivity Modern fleets operate in environments that demand far more from ...

From police AI to RTCC-led coordination, 5 public safety trends are changing modern policing and emergency response for faster, better ...
