An easier way to secure, assign, and manage user-to-resource access
Ericsson’s NetCloud SASE ZTNA solution is available as-a-service or as a customer hosted or hybrid model.
Zero Trust Network Access (ZTNA)
Trust is earned, not given. It’s why enterprise networking is moving beyond traditional firewalls, VPNs, and even modern perimeter-based security technologies. When extending remote access to employees and third parties, businesses need Zero Trust Network Access (ZTNA) technology that prevents lateral movements, limits user access to “just enough,” verifies before trusting, and never stops monitoring. Our ZTNA solution offers client and clientless options and easily integrates with your organization’s identity provider so you can build access policies that directly connect authenticated users with authorized resources — and nothing else.
Ericsson’s NetCloud SASE ZTNA solution is available as-a-service or as a customer hosted or hybrid model.
Improve your overall security posture with fully integrated firewall capabilities. Block unwanted traffic, detect and prevent intrusions, and ensure web traffic complies with organizational policies
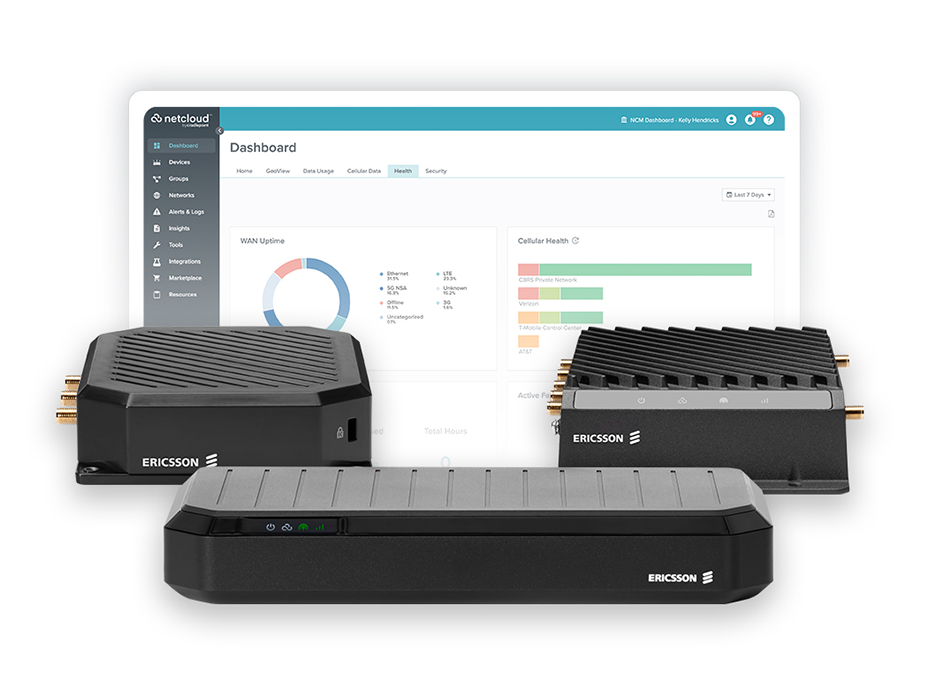
Ericsson NetCloud Manager provides full lifecycle management for Wireless WANs, including zero-touch deployment, creation of secure networks, and at-a-glance analytics and troubleshooting — enabling you to scale your network, not your staff.
